Transit Finance has pledged to compensate all affected users after an attacker drained approximately $1.88 million from a deprecated smart contract.
Security monitoring platform PeckShield flagged Transit Finance’s breach, stating that the stolen funds are currently parked in a $DAI address.
In an onchain message sent by Transit Finance to the attacker’s wallet, the attacker was informed that they may get a certain percentage of reward as a bug bounty if they are willing to cooperate in returning the assets.
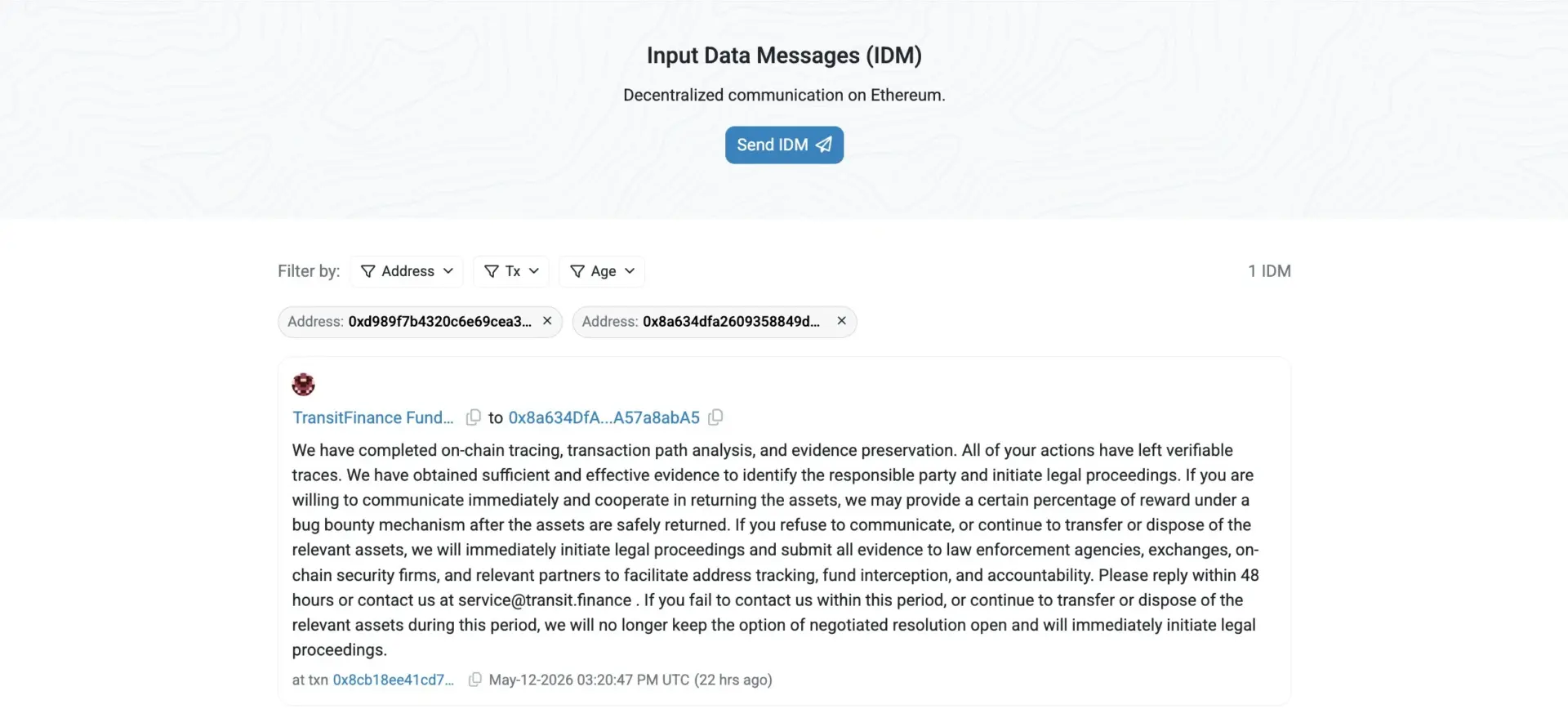 Transit Finance has sent a message with its hacker. Source: Etherscan.
Transit Finance has sent a message with its hacker. Source: Etherscan.
Transit Finance has set a 48-hour window for the attacker to respond, while adding that it will be providing further details on compensation through its official channels in another post.
What went wrong with Transit Finance?
Transit Finance attributed the breach to an early-version smart contract previously deployed on the TRON network.
In a statement posted to X, the protocol said the contract had been deprecated since 2022 but that “historical vulnerabilities within it were recently exploited, affecting a limited number of users.”
The team stated that it has carried out investigation, isolation, and mitigation measures upon discovery, followed by remediation on May 12. The protocol informed its users that they do not need to perform any further actions on their part.
It also stated that the current smart contract version remains unaffected and has been operating securely for over four years, with ongoing security audits and monitoring in place.
Crypto exploits in May
Transit Finance is not an isolated case, as security platform GoPlus Security announced on May 12 that it had flagged two private key compromise incidents over the preceding 36 hours, resulting in a combined loss of $238,000.
One involved trader @0xUnihax0r, lost $200,000 in what GoPlus linked to materials uploaded in connection with a trading bot and Telegram. The second compromised address was tied to a prior large-scale private key leakage event involving 574 addresses, suggesting the same exposure vector continues to claim victims weeks after the original incident.
Also on May 12, blockchain security company Blockaid issued a community alert on Aurellion Labs, a tokenized real-world asset protocol on Arbitrum. Blockaid wrote on X, “An unverified EIP-2535 Diamond proxy on Arbitrum was exploited a few minutes ago for ~$456K because of uninitialized Diamond / unprotected initialize().”
Taken together, the incidents of the first two weeks of May, Transit Finance, Aurellion Labs, and the GoPlus-flagged private key compromises, point to a month already accumulating losses across multiple vulnerability classes.
Can May be worse than April’s crypto exploit record?
The crypto space saw over $710 million in losses in April, with DeFi losing more than $609 million to cyberattacks.
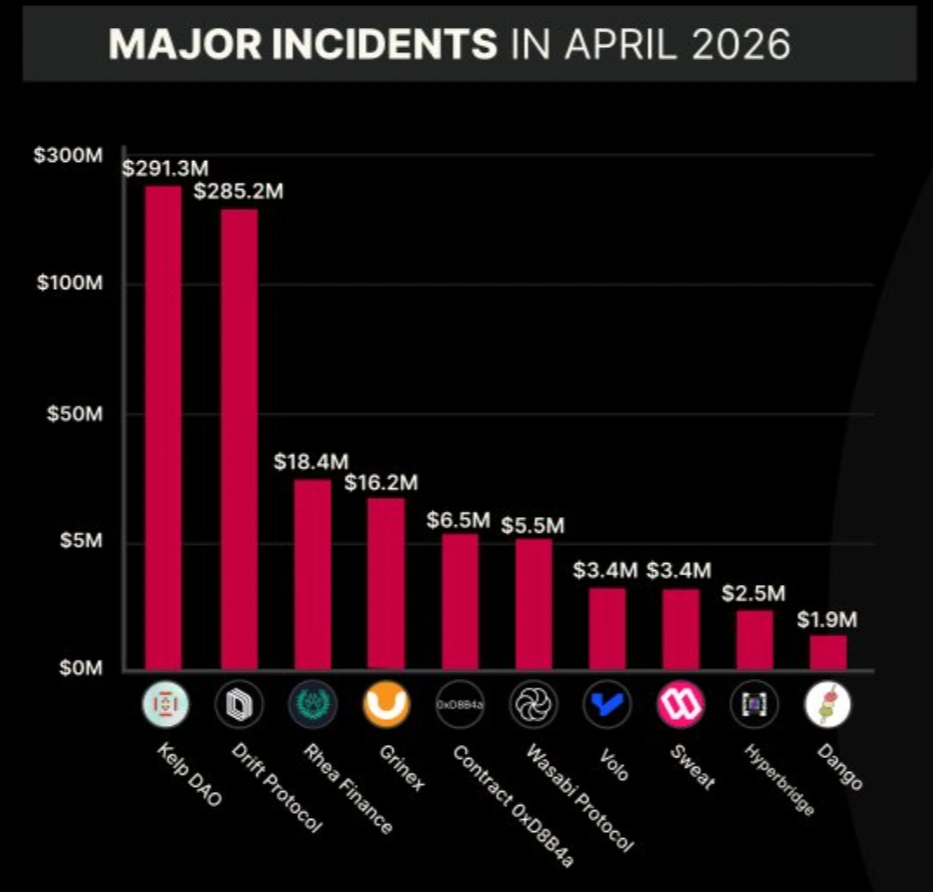 Major crypto hacks in April 2026. Source: CertiK.
Major crypto hacks in April 2026. Source: CertiK.
The KelpDAO exploit on April 19, which experienced a loss of $293 million from its LayerZero-powered bridge, was the largest DeFi incident of 2026. It was closely followed by Drift Protocol’s loss of $285 million, which occurred on April 1.
Drift Protocol’s hack was attributed to a long-running social engineering campaign by North Korean-affiliated actors, which came a close second.
May’s incidents are still considered smaller on an individual scale, as nothing so far approaches the nine-figure losses that defined April.
However, the frequency of the attacks is rising, and the month’s early cadence does not suggest that the sector has meaningfully addressed the conditions enabling these losses.
If you're reading this, you’re already ahead. Stay there with our newsletter.
















 English (US)
English (US)